What is Next Generation Secure Web Gateway?
A Next Generation Secure Web Gateway (SWG) is a new cloud-native solution for protecting enterprises from the growing volume of sophisticated cloud enabled threats and data risks. It is the logical...
What is Next Generation Secure Web Gateway?
A Next Generation Secure Web Gateway (SWG) is a new cloud-native solution for protecting enterprises from the growing volume of sophisticated cloud enabled threats and data risks. It is the logical...
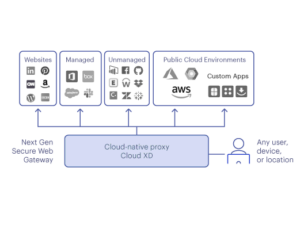
A Next Generation Secure Web Gateway (SWG) is a new cloud-native solution for protecting enterprises from the growing volume of sophisticated cloud enabled threats and data risks. It is the logical evolution of the traditional secure web gateway, also known as a web proxy or web filter. Unlike a traditional secure web gateway, a Next Gen SWG deals in both cloud and web traffic, whereas the former only deals in web traffic and is blind to cloud-enabled threats and data risks for personal instances of managed apps, thousands of shadow IT apps and cloud services. Over the past decade, many enterprises have allow listed specific cloud services such as Microsoft Office 365 to bypass inline firewall and proxy security defenses – enabling a “red carpet” entry for threats or data exfiltration. The inability to detect data transferring between company and personal cloud app instances or the use of rogue instances for threat cloud delivery adds to the list of blind spots for legacy defenses. Next Gen SWG allows you to continue to operate without sacrificing control over company data movement in apps and cloud services, or stifling workflows with blanket bans on certain applications and activities. This is crucial considering the recent and massive shift from office work to remote work, as well as the migration from traditional on-premise architectures over to the cloud during the past few years.
How is a Next Generation Secure Web Gateway Different from a Legacy Web Proxy Solution?
As stated earlier, Next Gen SWG is the next evolution in traditional web proxy gateway solutions, but how exactly do they protect against the modern threat landscape and data risks? Simply put, traditional web filtering and proxy solutions are no longer effective at safeguarding web and cloud app users or the enterprise from the following: Increasing cloud apps and services, as well as cloud-enabled threats More than half of web traffic today (53%) is related to apps and cloud services, and more than two-thirds of malware (68%) is delivered from cloud apps versus the web*. Legacy web proxy gateways cannot decode apps and cloud services to detect these cloud delivered threats. All stages of the cyber kill chain are now cloud-enabled, including reconnaissance, weaponisation, delivery, and call back communications. Business units and users continue to freely adopt new apps and cloud services, growing 22% for the first six months of this year where the average company with 500-2000 users accesses 805 distinct apps. Legacy SWG solutions are mostly blind to these growing shadow IT apps and cloud services and less than 3% are managed by IT. Rising data exposure and theft in a cloud-first world Over 90% of data created in the cloud happened in the last two years and more than 70% of users are mobile and work remotely. The ability to transfer data between company and personal instances of managed cloud apps, or to another personal cloud app instance, plus using webmail and sharing links is an easy task for any user today. Growing number of remote workers accessing private and public apps and resources The digital transformation to cloud and mobile is inverting the legacy appliance-based security stack to the cloud to better protect an increasing base of remote workers. Legacy SWG appliances located in offices force traffic hair-pinning with VPNs to central data centres which is no longer sufficient and results in a poor user experience. Secure access service edge (SASE) architecture unites multiple security defenses into one cloud platform, with one console, and one policy engine resulting in lower total cost of operations. Next Gen SWGs cover five lanes of user traffic to public resources including web, managed SaaS, shadow IT, public cloud services, and custom apps in public cloud services. Private apps and resources within SASE architecture use Zero trust network access (ZTNA) where implicit trust based on location or device is removed. In this new model, any user, any location, on any device is protected by a nearby cloud security services edge with minimal impact on performance. What makes a Next Gen SWG truly “next generation” is the depth of control, monitoring, and protection for the five lanes of user traffic inspected. A Next Gen SWG goes beyond old “allow/block” policies of web proxies for one-lane of traffic and combines the capabilities of proxies, inline cloud access security brokers (CASB), and data loss prevention (DLP) platforms. This combination delivers a variety of advanced cloud visibility features and capabilities:
- web content filtering with dynamic ratings
- SSL/TLS decryption with cloud performance and scale
- cloud access security broker (CASB) inline functionality to discover, decode and inspect apps and cloud services traffic
- advanced threat protection (ATP) including sandboxing and machine learning-based anomaly detection
- data loss prevention (DLP) for cloud apps and web traffic
- insights, rich metadata context for investigations, detailed reporting, and more.
With the use of a Next Gen SWG, you can monitor behaviour for web, apps and cloud services, set granular acceptable use policies, invoke adaptive policies based on app risk, user risk, activity, and data sensitivity, and provide real-time user coaching to safer alternatives and away from risky apps. Not only does this improve your security in the cloud, but it also improves user experiences by avoiding blanket bans on certain actions and devices. Granular controls and inline visibility of a Next Gen SWG helps contextualise user and data activity so adaptive policies can guide users while reducing risk and protecting data without interfering with legitimate work practices.
What are the Common Next Gen Secure Web Gateway Capabilities?
These are the six individual capabilities unique to a Next Generation Secure Web Gateway: Monitors and assesses individual actions Achieve inline visibility for thousands of managed and unmanaged apps and cloud services, plus web traffic, and unify SWG+CASB+DLP critical capabilities into one platform. Granular control over applications Get real-time, granular control of thousands of cloud apps including the shadow IT ones led by lines of business and users vs. IT. This enables you to stop the bad stuff from happening and safely enable the good. Implementation of acceptable use policies Incorporate a combination of traditional web filtering covering URL categories, custom categories, and dynamic page ratings for new sites with comprehensive cloud app usage ratings, risks, and acceptable use policies that cover both cloud and web. Protection against threats Protect against web and cloud-delivered malware and advanced threats with advanced defense capabilities from cloud app instance awareness to detect rogue and personal instances used to deliver phishing and threats, to pre-execution analysis of scripts and macros, cloud and bare-metal sandboxing, and machine learning-based threat analysis and anomaly detection. Protection of data everywhere Follow and protect data everywhere it goes and ensure accurate and precise inspection with advanced capabilities ranging from exact match to fingerprinting with similarity matching. Covers direct-to-internet Eliminate costly back hauling and improve performance for remote offices and users with cloud edge-based network infrastructure, optimised for low latency and high capacity worldwide.
What to Look for in a Next Gen Secure Web Gateway
Organisations looking to adopt a Next Gen SWG should look for a single-platform, unified, cloud-native solution that: Leverages true cloud architecture The solution must be built around cloud-native microservices with fully integrated capabilities, not cloud-hosted separate legacy solutions, for true cloud performance and scale. Also, using a carrier grade private network optimised for access leveraging peering relationships with global and local cloud service providers is essential for worldwide availability and performance. The resulting cloud service has a minimal performance impact on the user experience, and in some cases, an accelerated experience. Decodes apps and cloud services The solution must decode thousands of apps and cloud services alongside web traffic to understand content and context for data and threat protection defenses. The new language is APIs built around JSON for apps, cloud services, and web sites. NG SWG defenses need to understand user, device, location, app, risk, instance, content, and activity for contextual policy controls, plus collecting rich metadata for analytics, investigations and machine learning. Keep pace with new attacks The solution can’t simply protect against known attacks, instead, it should be able to address a wide array of new and emerging threats, including cloud-enabled threats such as cloud phishing, cloud payload delivery, and callback communications. This requires the systematic advantage of decoding apps and cloud services for content and context for advanced threat and data protection defenses, plus machine learning. Cloud-enabled threats leverage trusted domains with valid certificates either passing through legacy defenses or being allow-listed to bypass defenses. Users can maliciously or accidentally transfer data between company and personal instances, or be phished for access credentials in these legacy environments.
What’s the Role of Next Gen SWG in a SASE Dominated Future?
With the massive shifts to the cloud over the course of the pandemic, SWG technology is morphing into something bigger than itself. Combined with other technologies such as data loss prevention (DLP) and Cloud Access Security Brokers (CASB), the concept of a Next Gen Secure Web Gateway is a crucial component of what is known as Secure Access Service Edge (SASE) architecture. SASE combines multiple security and networking technologies to provide comprehensive web and cloud security without the hiccups of traditional perimeter appliance-based security, such as latency and lack of context into data usage. What this means is that a limited scope solution like a secure web gateway is no longer an option for companies. It’ll require a combined approach of multiple tools in which Next Gen SWGs are just a component of this security strategy.


.svg)
.png)
